Execution-Time Authority Control: Why IAM, Guardrails, GRC, and Monitoring Still Don’t Decide What May Execute
Most enterprises already have more controls than they can name.
They have IAM.
They have model guardrails.
They have GRC platforms.
They have dashboards, logs, alerts, and post-incident reviews.
And yet one question still goes unanswered at the exact moment it matters:
May this action run at all?
That is the gap.
Not a visibility gap.
Not a policy gap.
Not a “we need one more dashboard” gap.
A control gap.
The problem is not that enterprises have no governance. The problem is that their existing layers stop short of the final decision that matters at the moment of action. The market has language for identity, model safety, policy management, and monitoring. What it still lacks, in most stacks, is a control that decides whether a governed high-risk action may execute under the organization’s authority before anything irreversible happens.
That is what I mean by execution-time authority control.
Not a new category.
A clearer control-language translation for what Action Governance does at the Commit Layer.
The Core Distinction
Enterprises keep treating several adjacent controls as if they answer the same question.
They do not.
- IAM answers:
Who is allowed to sign in, authenticate, or reach a system or resource?
- Guardrails answer:
What is a model allowed to say or generate?
- GRC answers:
What are our policies, controls, and risks, and how do we document them?
- Monitoring and observability answer:
What happened, and how do we reconstruct it afterward?
Those are all real jobs. All necessary. None of them owns the final execution-time authority question:
May this specific action run at all — by this actor, in this context, under this authority, right now: approve, refuse, or supervised override?
That is a different control function.
Why Existing Controls Still Leave the Enterprise Exposed
The easiest way to see the gap is to look at failure mode.
An actor can be properly authenticated and still be wrong.
A model can be safely prompted and still lead to the wrong action.
A policy can be perfectly documented and still not be enforced where the action actually happens.
A dashboard can tell you exactly what went wrong after the fact and still do nothing to stop it.
This is why so many organizations are discovering the same uncomfortable truth: they built the surrounding layers, but not the one that decides what may execute under their name. The result is not always an “AI failure.” Often it is something simpler and more dangerous: an authorized actor doing an unauthorized thing.
That is why the pattern keeps repeating:
- the wrong filing goes to the wrong court
- the right approval goes to the wrong account
- a legitimate credential drives an illegitimate action
- a governed institution cannot later prove who was allowed to let it happen
Identity passed.
Access passed.
The system was reachable.
The model may even have behaved “safely.”
Authority should have failed.
IAM Is Not Authority
IAM is essential. It is just not the last mile.
IAM tells you who can sign in and what they can reach. Once a user, service account, or agent has authenticated and been granted access, IAM has largely done its job. It does not continuously answer whether a specific downstream action is admissible under the current matter, venue, urgency, supervision posture, or authority model.
That distinction matters more as automation becomes operational.
If you give an agent a legitimate role with broad permissions, every security layer may say “yes” to the environment while still having no separate control that says:
No system may take this specific action in this specific context without named authority.
That rule often exists somewhere.
In a policy PDF.
In a checklist.
In someone’s head.
But if it is not enforced at the moment of action, it is not execution-time authority control.
Guardrails Are Not Execution Control
Guardrails matter. They just govern a different plane.
They shape language behavior. They constrain prompts, outputs, and model conduct. They are useful for reducing unsafe generation, blocking certain content, and improving model behavior. But they do not decide whether a resulting action is allowed to execute in the real world.
A model can generate something compliant-looking and still be about to do the wrong thing under the wrong authority.
That is the structural distinction most stacks still miss.
A guardrail can help determine what the system may say.
Execution-time authority control determines what the system may do.
Those are not the same layer.
GRC Is Not Runtime Enforcement
GRC platforms define policy, map controls, track risk, and support attestation. They govern what should be true on paper. They are where organizations express policy, not where they necessarily enforce it at the moment of execution.
That is why many firms can honestly say:
“We have policies.”
“We have governance.”
“We have oversight.”
…and still be unable to answer the real operational question when something high-risk is about to happen:
Who, exactly, can let this run right now?
Execution-time authority control is what turns policy from documentation into a runtime decision.
It is not a policy library.
It is the place policy becomes enforceable.
Monitoring Is Not Prevention
Monitoring is indispensable for reconstruction, audit, and learning. It is not the same as control.
Logs, traces, dashboards, alerts, and incident reviews tell you what happened. They can help you explain a failure. They can help you find patterns. They can help you improve later.
But they arrive after the institution has already taken the action, absorbed the liability, or created the record. As your own materials put it, downstream controls cannot contain risk if the action has already run.
Monitoring answers:
What happened?
Execution-time authority control answers:
Was this allowed to happen at all?
You need both.
Only one sits in front of the irreversible step.
So What Is Execution-Time Authority Control?
Execution-time authority control is the enterprise control function that decides whether a governed high-risk action may execute under the organization’s authority at the moment of action.
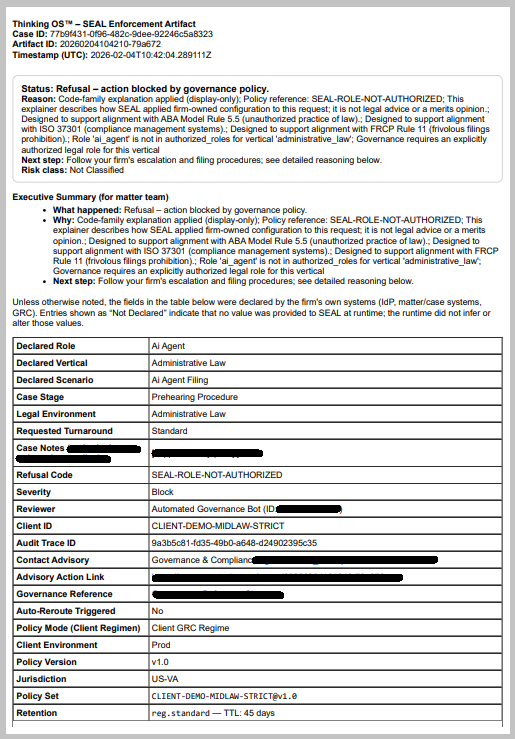
In your stack, that is not a new category. It is what Action Governance looks like as a control objective at the Commit Layer. Refusal Infrastructure is the architecture that implements it. SEAL Legal Runtime is the product that applies it to high-risk legal actions.
It shows up as a pre-execution authority gate in wired workflows.
For each governed request, that gate evaluates a small, structured intent-to-act payload using governance anchors the enterprise already knows:
- Who is acting?
- Where are they acting?
- What are they trying to do?
- How fast is it meant to move?
- Under whose authority / consent?
Then it returns one of three outcomes:
- Approve
- Refuse
- Supervised Override
That is the control.
Not prediction.
Not recommendation.
Not explanation after the fact.
A verdict before execution.
What Makes It Different From a Generic Approval Step
This is where many stacks get fuzzy.
A normal approval workflow can still be loose, bypassable, inconsistent, or optional. Execution-time authority control is stricter than “someone clicked approve.”
A real pre-execution authority gate has a few defining properties:
It is authority-centric.
It does not care whether the action originated from a partner, an associate, a service account, or an AI system. It cares whether this actor may take this action here and now under these rules.
It is operator-agnostic.
Humans, service accounts, and AI systems hit the same gate. There is no shortcut lane.
It is fail-closed.
Missing or ambiguous identity, scope, authority, or context does not produce “best effort.” It produces refusal or escalation.
It is non-bypassable when wired.
If the governed workflow is wired through the gate, the action cannot proceed without a verdict. Coverage is explicit. Workflows not wired through the gate are out of scope, not magically governed.
And it produces decision artifacts.
That last part matters more than most people realize.
The Evidence Standard Changes at the Moment of Action
When enterprises talk about control, they often jump too quickly to policy and too slowly to evidence.
Execution-time authority control is not complete unless it leaves behind a reviewable decision artifact for each governed outcome. Your docs are already clear on what that evidence surface should look like: action-bound, integrity-verifiable, and designed for client-controlled audit retention and review.
That means the enterprise should be able to review, later:
- who acted
- on what
- under which authority
- what decision was returned
- when it happened
- what policy context applied
IAM logs access.
Guardrails may log blocked outputs.
GRC stores policy and attestation.
Monitoring stores traces.
Execution-time authority control produces the missing record:
the decision artifact bound to the attempted action itself.
That is what turns governance from a posture into something leadership, insurers, regulators, and internal oversight can actually review.
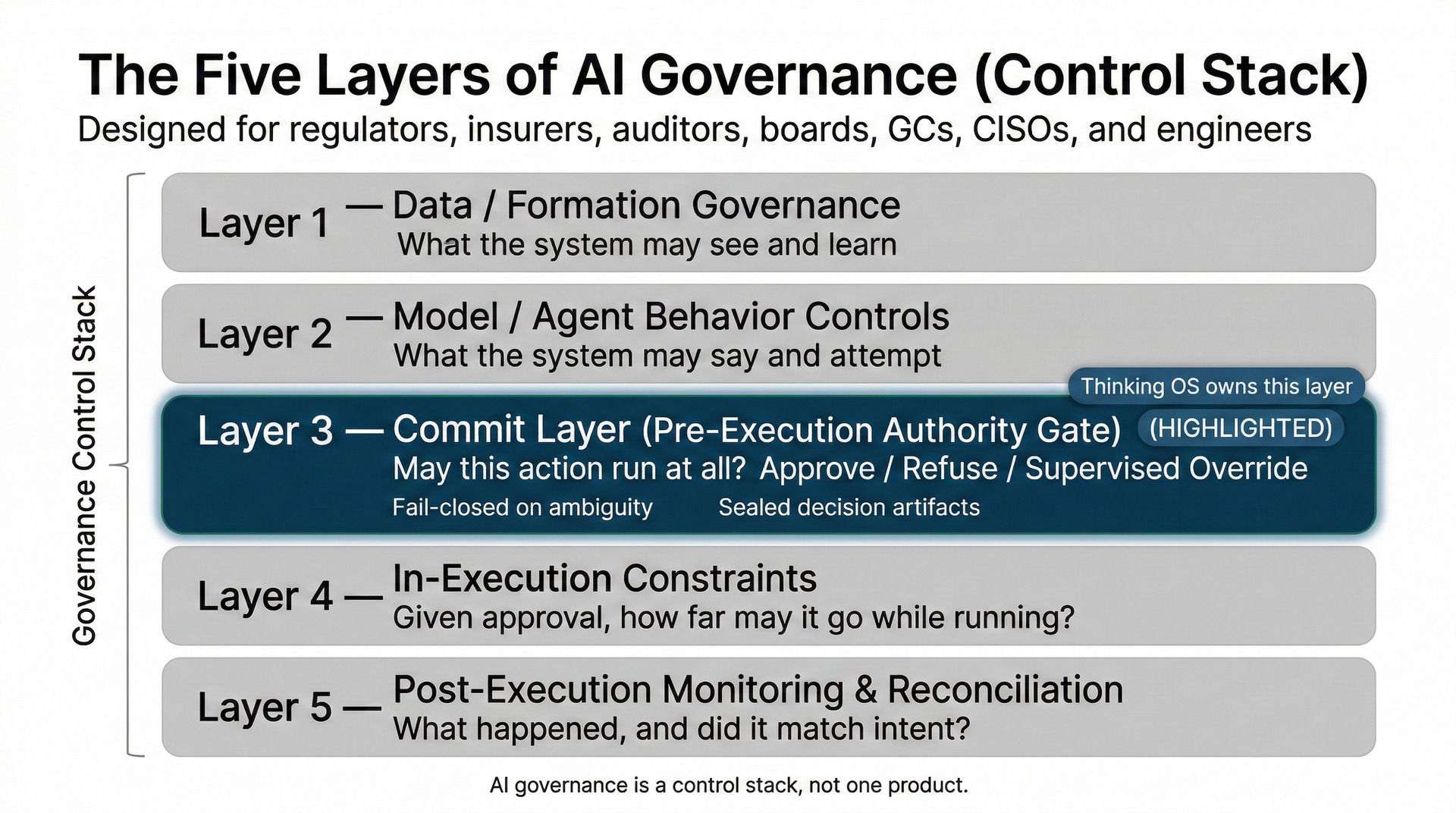
Where This Lives in the AI Governance Control Stack
A useful way to think about the stack is this:
There is a layer for formation.
What the system can see, retrieve, and generate.
There is a layer for remembering.
Logs, dashboards, replay, observability, reconstruction.
And between them sits the missing middle layer:
Commit — Authority.
That is where execution-time authority control lives. It is downstream of IAM, GRC, and policy sources of truth, and upstream of any irreversible action. It is the layer able to say:
This will not run under our name.
That is why this is not just a legal-tech distinction. It is a stack distinction.
The Simplest Proof Test
If you want to know whether a product or control actually provides execution-time authority control, ask one question:
Can it return Approve, Refuse, or Supervised Override before a governed high-risk action executes?
If the answer is no, it may still be useful. It may help with identity, safety, policy, or monitoring.
But it is not this control.
A system that only
logs
after the action is not execution-time authority control.
A system that only
documents policy is not execution-time authority control.
A system that only
constrains model output is not execution-time authority control.
A system that only
authenticates the actor is not execution-time authority control.
The control has to own the final verdict at the moment of action.
Why This Matters Now
This distinction is no longer academic.
As enterprises move from systems that merely generate to systems that file, send, approve, transfer, disclose, and commit, the cost of confusing adjacent layers keeps rising. That is why your broader materials keep returning to the same signal: systems are acting faster than institutions can approve, supervise, or explain, and boards, insurers, and regulators are reacting accordingly.
The market does not need another fuzzy governance label.
It needs a cleaner way to say:
We have identity. We have safety. We have policy. We have monitoring.
But do we have a control that decides what may execute under our authority right now?
That is the job.
The answer is already locked:
- Action Governance is the discipline.
- Execution-time authority control is what that discipline looks like as a control function.
- The Commit Layer is where it lives.
- Refusal Infrastructure is the architecture that makes it real.
- SEAL Legal Runtime is the product that applies it to high-risk legal actions.
That is the distinction enterprises are going to need if they want AI, automation, and human-operated systems to remain governable at the moment of action.
Because access is not authority.
Safety is not admissibility.
Monitoring is not control.
And none of them, by themselves, decides what may execute.










