Verifier Note
How to Validate a Sealed Decision Artifact Without Trusting the Vendor
Reference Note — for regulators, insurers, auditors, procurement, and technical evaluators
Status:
Public verifier note
Scope: What an evaluator should be able to verify from a sealed decision artifact, without access to vendor internals
1. Purpose
A sealed decision artifact is useful only if a third party can review it as evidence, not just as vendor output.
This note explains what a qualified evaluator should be able to validate from a sealed decision artifact without needing to trust vendor narratives, dashboards, or private explanations.
The goal is modest and practical:
- confirm that a governed decision actually occurred
- confirm what decision was recorded
- confirm the decision is tied to a specific context and policy version
- confirm the record is integrity-protected and suitable for tenant-controlled retention
- confirm what can and cannot be concluded from the artifact alone
This note is intentionally evaluator-facing. It is
not a deployment guide, cryptographic specification, or implementation manual.
2. What a Verifier Should Be Able to Confirm
A sealed decision artifact should allow an evaluator to confirm, at minimum, the following categories of fact.
A. Artifact identity
The artifact should carry a stable identifier and timestamp so it can be referenced, sampled, and compared across systems and review periods.
Examples of reviewable fields include:
- artifact ID or decision ID
- case or request identifier
- timestamp
- audit trace or correlation identifier
These fields let an evaluator answer a basic question:
Is this a concrete recorded decision, or just a screenshot or narrative summary?
B. Outcome
The artifact should clearly state the governance outcome.
At minimum, the evaluator should be able to tell whether the runtime recorded:
- Approve
- Refuse
- Supervised Override
The outcome must be visible as a governance result, not buried inside technical error language.
C. Context anchors
The artifact should show enough structured context to explain what was being governed.
A verifier should expect to see a practical subset of the decision anchors, such as:
- who was acting
- what action or scenario was attempted
- where the action was situated
- relevant urgency / deadline / turnaround context
- authority / consent / supervision posture as applicable
D. Policy linkage
The artifact should identify the governing rule surface in force at decision time.
A verifier should expect to see references such as:
- policy set
- policy version
- refusal or override code
- decision stage or governance engine label
- high-level rule-basis reference
This is what allows an evaluator to ask:
Which policy set governed this decision, and can historical decisions be tied to the version in force at the time?
E. Integrity evidence
The artifact should provide a way to detect tampering.
Public materials do not need to disclose the full mechanism. But an evaluator should expect visible integrity-oriented elements such as:
- refusal hash / artifact hash / integrity proof
- append-only audit retention statement
- tenant-owned audit storage reference
- verification or audit linkages
Example Sealed Decision Artifact (Redacted)
The following image is a redacted example of a refusal artifact generated by a pre-execution governance runtime.
It illustrates the type of fields evaluators should expect when reviewing a decision artifact.
Verification Example — Redacted Sealed Decision Artifact
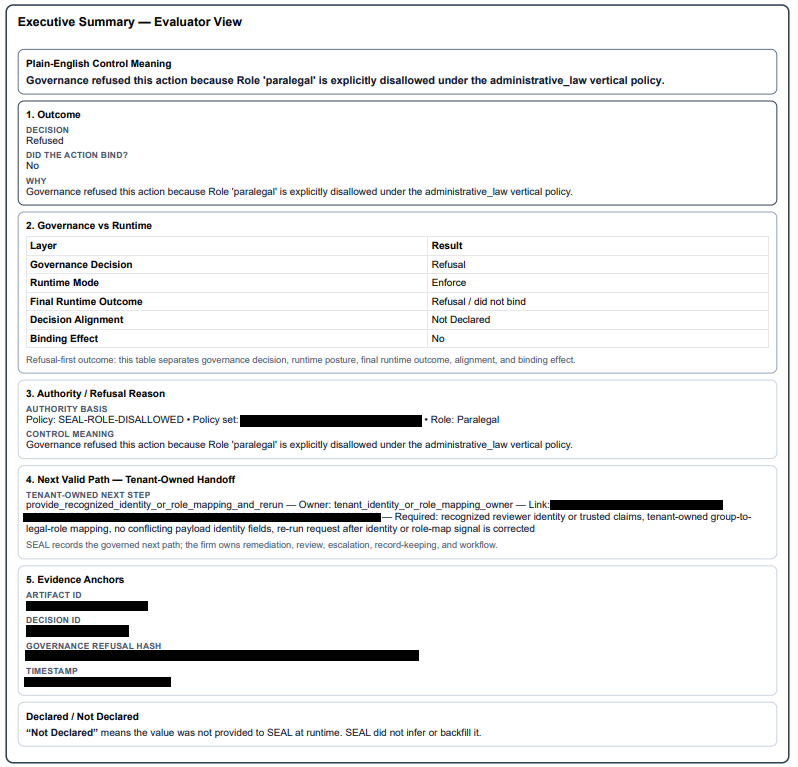
Note: This example is illustrative. Actual artifact formats vary by deployment, but the verification properties described above should remain consistent.
Redacted artifact example. Fields unrelated to verification have been removed.
3. What Cannot Be Verified From The Artifact Alone
A sealed decision artifact does not by itself prove:
- that the tenant’s policy was wise or legally correct
- that every workflow in the environment was governed
- that upstream identity or matter systems were correct
- that the runtime’s internal rule graph or execution logic was sound
- that no unwired path existed elsewhere in the environment
- that the artifact should be interpreted as legal advice
An artifact proves that a specific governed decision was recorded, with specific anchors, under a referenced policy version, with integrity controls suitable for later review.
That is its role, and it is a meaningful one.
4. Minimum Evaluator Procedure
A practical evaluator procedure should be simple and repeatable.
Step 1 — Inspect identity and correlation fields
Confirm the artifact contains a stable identifier, timestamp, and correlation fields sufficient for sampling and cross-reference.
Step 2 — Confirm the verdict
Check that the artifact plainly records one governance outcome: approve, refuse, or supervised override.
Step 3 — Check the anchor set
Confirm the artifact contains enough structured context to explain the governed attempt at a practical level: actor, action, context, policy reference, and relevant authority or timing posture.
Step 4 — Check policy linkage
Confirm the artifact references the policy set, policy version, and reason or refusal family that governed the decision.
Step 5 — Check integrity indicators
Confirm the artifact includes an integrity proof or equivalent integrity-verifiable field and is stated to be retained in tenant-controlled, append-only audit storage with integrity controls.
Step 6 — Sample across decision types
Review not just one refusal. A serious evaluation should sample:
- an approval
- a refusal
- a supervised override, if applicable
This helps confirm that outcomes are functioning as governance results rather than cosmetic labels.
5. What a Vendor Should Be Able To Demonstrate In Diligence
Without exposing proprietary internals, a vendor should still be able to support a meaningful review.
A qualified evaluator should be able to request:
- redacted sample artifacts across outcome types
- explanation of required artifact fields
- policy-version linkage at a high level
- explanation of what is tenant-controlled versus vendor-controlled
- a verifier workflow showing how integrity checks are performed
- a coverage statement clarifying wired workflows versus out-of-scope paths
That is enough to evaluate whether the runtime produces
evidence-grade decision records, not just operational logs.
6. What This Note Is Not
This note is not:
- a full artifact schema
- a cryptographic disclosure
- a key-management description
- a deployment architecture diagram
- a rule-engine specification
- a client implementation guide
- a statement that all workflows are governed
It is a public verifier note: a description of what an evaluator should be able to check independently.
7. Why This Matters
The difference between ordinary logging and a sealed decision artifact is not formatting. It is evidentiary posture.
.
Ordinary logs help reconstruct events after the fact.
A sealed decision artifact helps show:
- what action was being governed
- what the runtime decided
- which policy surface was applied
- whether the record has been altered since issuance
That is why regulators, insurers, auditors, and procurement teams care about this evidence surface.
The core question is not whether a vendor says it has governance.
The core question is:
Can a third party review a decision record and validate that a real governed decision occurred, in a real context, under a referenced policy version, without depending entirely on vendor trust?
That is the purpose of the sealed artifact.
That is what this note is designed to make testable.

