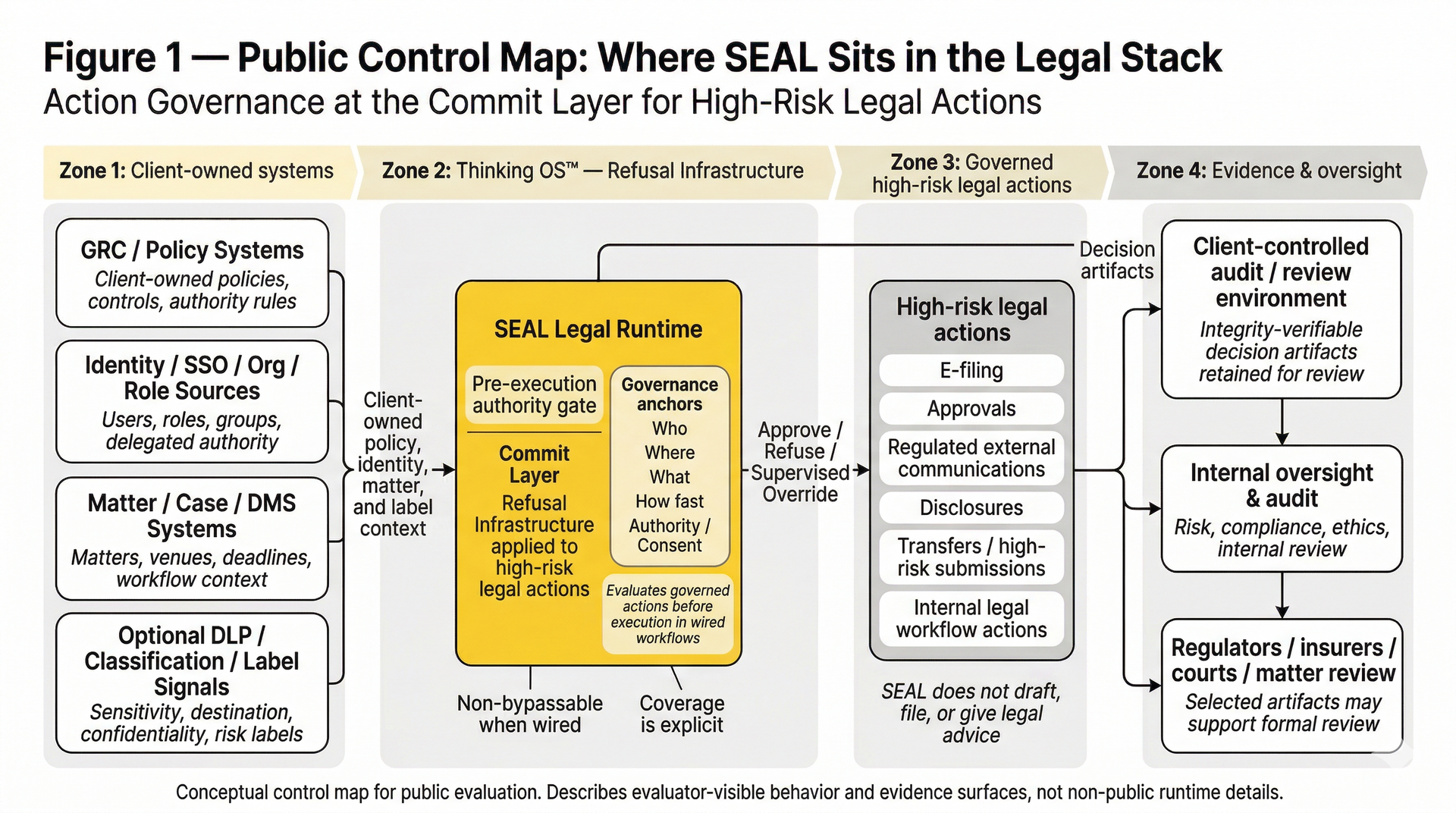
Refusal Infrastructure for High-Risk Legal Actions
Thinking OS™ is the platform and public framework for Refusal Infrastructure in legal: a governance runtime pattern that inserts the missing Commit Layer — a pre-execution authority gate for high-risk legal actions.
SEAL Legal Runtime is the product that applies this pattern in law.
It decides whether a designated action may proceed, must be refused, or requires supervised override before anything is filed, sent, approved, or otherwise made real. It applies the same governance posture across humans, AI systems, service accounts, and workflows.
A seatbelt for governed actions.
→
Thinking OS™ decides whether a designated action may proceed, must be refused, or requires supervised override — and produces a reviewable decision artifact either way.
Works Across Humans, AI, and Workflows
Thinking OS™ applies the same governance posture to any actor that initiates a governed action:
• a human operator
• an automated workflow
• an AI system or service account
Capability may differ. Authority checks do not
Where the Commit Layer Sits in the Stack
Thinking OS™ sits at the execution boundary — between your client-owned systems and designated high-risk actions routed through SEAL Legal Runtime.
Client-owned systems (you)
- GRC / policy systems – your firm policies and risk rules
- Identity / SSO / org chart – your users, roles, and groups
- Matter / case systems – your courts, venues, and deadlines
SEAL Legal Runtime — Commit Layer / Pre-Execution Authority Gate
• Uses your identity, matter, and policy systems as sources of truth
• Evaluates governed requests at the moment of action
• Returns Approve, Refuse, or Supervised Override
• Produces reviewable decision artifacts for each governed outcome
Internal tools & workflows (you)
- AI tools, drafting tools, automation, e-filing, portals
- These only run after Thinking OS™ has cleared the action
Destinations & oversight
- Courts and regulators – filing packets may include SEAL artifacts
- Internal oversight & audit – risk, ethics, and compliance teams review artifacts as needed
It acts as a governance gate in front of your “file / submit / act” buttons for the workflows that call it. It never replaces your systems; it gates them and produces sealed evidence of what it did. When you wire it as the only path to a given action, every request on that path is evaluated under the same checks.
Coverage is explicit, not implied: workflows not wired through the gate are out of scope by definition and should be treated as uncovered risk.
What Flows Through It
For each governed request, your systems send a small, structured payload—essentially “intent to act”.
Every governed request carries the minimum governance context SEAL needs to evaluate authority:
- Who is acting?
Partner, associate, staff, AI agent, or system account - Where are they acting?
Practice area / vertical (e.g., civil litigation, bankruptcy) - What are they trying to do?
Specific action or motion (e.g., file motion to dismiss) - How fast is it meant to move?
Standard, expedited, emergency - Under whose authority or consent?
As defined in your own policies and authorities
Those inputs come from your identity, GRC, and matter systems.
Thinking OS™ does not invent roles, policies, or authority.
It evaluates governance anchors, not the substance of your client work.
What Happens at Runtime
When a tool or workflow wants to take a governed action:
- Your system calls Thinking OS™ with who/where/what/how fast/consent.
- Thinking OS™ checks that request against your rules and licenses:
- identity and role
- vertical / practice scope
- motion / action type
- urgency
- consent / authority
3. If everything is in bounds, the action is approved and your tools proceed as they do today.
4. If something is off or unclear, the action is refused or routed for supervision before anything goes out the door.
Design Posture (from the SEAL runtime):
- Single governance path for wired workflows – every request that reaches SEAL goes through the same checks; overrides run through the same engine and cannot silently skip policy.
- Fail-closed by design – unknown roles, missing consent, broken evidence, or uncertainty → sealed refusal, not silent pass.
- Bounded integration – SEAL adds an execution-time control point without replacing your existing systems.
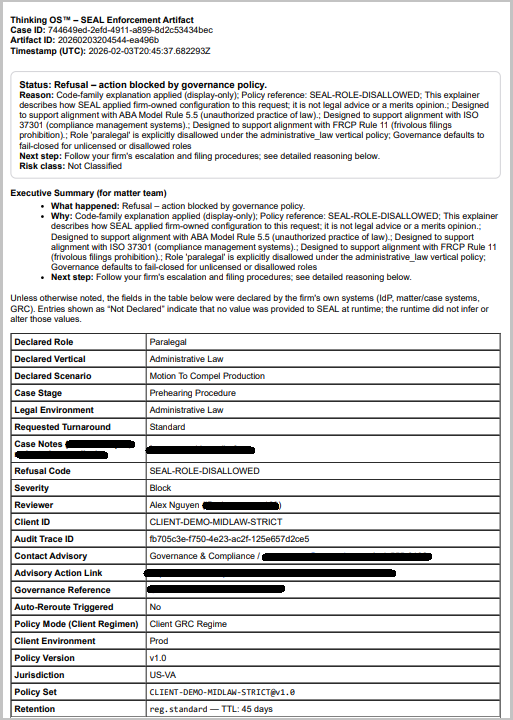
What Comes Out: Sealed Artifacts
Every approval, refusal, and supervised override generates a decision artifact, not just another log line.
Representative artifact elements include:
• a decision / trace reference
• the governance anchors in force
• the governing policy or rule-basis reference
• the verdict returned
• a short human-readable rationale
Firms typically:
- Attach approval artifacts to matters
- Route refusal artifacts to the right teams for supervision
- Produce relevant artifacts in regulator, insurer, or bar packets when asked
For legal, this becomes evidence-grade governance documentation designed to withstand regulator, insurer, and court scrutiny — without exposing client matter content or model prompts.
Sealed Artifact, Not a Screenshot
Example refusal artifact (simulated realism testing).
A paralegal role attempted to file in a venue requiring licensed counsel. The pre-execution authority gate refused the action and produced a decision artifact showing:
• who attempted the action
• what governed action was attempted
• which policy context applied
• why the request was refused
This is the evidence surface firms can use for insurers, regulators, courts, and internal review — without exposing client matter content or model prompts.
Why The Commit Layer Exists
Most AI and workflow systems govern after the fact — through logs, dashboards, or retrospective review after the action has already happened.
High-risk legal actions cannot rely on reconstruction after execution.
SEAL exists to answer one upstream question:
“May this specific action run at all, under this authority, in this context, right now?”
That runtime discipline is
Action Governance.
The
Commit Layer is where it lives.
Why It Matters
Most systems are optimized for speed or capability.
Thinking OS™ is optimized for governability:
•
Bounded — actions constrained by role, context, and authority
•
Traceable — decision artifacts show what was allowed, refused, or escalated
•
Refusable — unsafe or out-of-policy actions are blocked before execution
In legal and other regulated environments, speed without authority control is exposure.
Thinking OS™ builds Refusal Infrastructure.
SEAL Legal Runtime applies it to high-risk legal actions.
Not another model.
Not another dashboard.
A pre-execution authority gate for moments where decisions must stand up to courts, regulators, insurers, and time.

