SEAL Legal Runtime
Stop the Wrong Legal Filing Before It Leaves Your Firm
SEAL sits in front of your final filing step and either approves, refuses, or routes for supervision
before a motion or submission leaves your firm.
If the wrong actor tries to file under the wrong authority,
SEAL says no before the court or regulator ever sees it.
Approve. Refuse. Supervise.
Fail closed when required conditions are missing or cannot be safely evaluated.
One Governed Checkpoint At Your Final Submit Boundary
You do not need another drafting tool, case system, or general-purpose AI guardrail.
You need one enforceable checkpoint before a high-risk legal action leaves your firm.
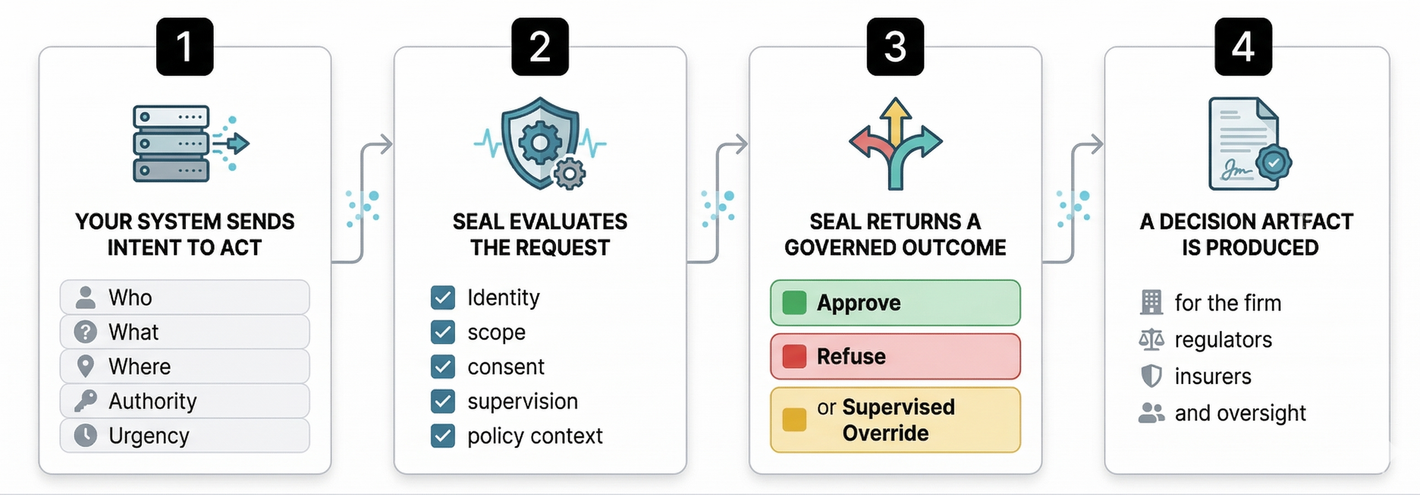
SEAL inserts that checkpoint at the final file or submit step. Your existing systems remain your sources of truth for policy, identity, matter context, and supervision. SEAL evaluates whether the filing or submission may proceed under those conditions and returns one governed outcome before the action executes.
Every governed outcome produces a sealed, reviewable decision artifact showing what the control did at the moment of action.
SEAL can refuse. It cannot file.
Where SEAL Sits In Your Workflow
SEAL runs behind the scenes as an upstream control layer. Your lawyers and staff keep working in the systems they already use.
This is not after-the-fact monitoring. This is a control point at the moment before execution.
What You Can Verify Quickly
You do not have to take this on faith. For the workflow in scope, you can verify:
- Approval exists
- Refusal exists
- Supervision exists
- Sealed decision artifacts exist
- Fail-closed behavior exists
- The downstream gate exists
- Scoped non-bypassability exists
This is the difference between a concept and a real pre-execution control.
Proof Before Promises
SEAL is not a chat wrapper, a dashboard, or a policy slideshow.
You can review where SEAL sits in the workflow, how the runtime returns governed outcomes, what refusal looks like before harm, how sealed artifacts are produced, and how downstream handling aligns to the governed decision.
You can review:
- A real approval artifact
- Real refusal artifacts from different refusal families
- A supervised escalation / override path
- Execution receipts tied to the same governed outcome
- A scoped non-bypassability proof for the workflow in scope
When SEAL refuses a governed action, it produces a sealed decision artifact showing who attempted the action, what was attempted, which policy context applied, and why the action was blocked.
You do not need exposed internals to evaluate whether the control is real. You need outputs you can review.
A Pilot You Can Safely Say Yes To
Your first pilot should feel narrow, bounded, and reversible.
We are not asking you to replace your systems or change legal practice overnight. We are asking you to place one sealed gate in front of one high-risk action boundary so you can evaluate whether the control works, whether the artifacts are useful, and whether the workflow remains operationally safe.
Pilot structure
- One governed workflow only
- One final file / submit boundary only
- One workflow owner
- One narrow role / authority scope
- One clear review cadence
You can start in observe-only mode, require supervised escalation, or move to active enforcement when you are ready.
You have clear pause, rollback, and stop conditions from the start.
Straight Answers To Your Trust Questions
Q1 — Is SEAL vendor-hosted?
Yes. SEAL is delivered as a vendor-hosted sealed API. Your systems call SEAL through an authenticated integration surface, and SEAL returns governed outcomes and decision artifacts.
Q2 — Why are the internals sealed?
Because the assurance model is inspectable behavior, not exposed internals. Evaluators review scenarios, governed outcomes, and sealed artifacts without exposing your systems or ours.
Q3 — What data does SEAL actually see?
Only the minimum structured governance signals required to evaluate the governed action: who is acting, what action is being attempted, what workflow or legal environment is involved, under what authority or consent posture, and any configured evidence, deadline, or rule-basis reference.
Q4 — Who owns policy and artifacts?
You own your policy, identity and role sources, matter context, workflow scope, supervision posture, and artifact retention. You control how your artifacts are used and retained.
Q5 — What happens if SEAL cannot safely evaluate a request?
SEAL fails closed. If a governed request cannot be safely evaluated, unsafe uncertainty does not become silent approval.
Q6 — Does SEAL replace legal judgment?
No. SEAL does not draft, file, give legal advice, decide litigation strategy, or replace professional supervision. It enforces your rules at runtime.
Without The Gate, Risk Is Invisible.
With the Gate, Near-misses Become Measurable.
SEAL does not just block certain bad actions. It gives you a measurable ledger of prevented loss events, supervised overrides, refusal reason codes, policy coverage, and downstream alignment.
That changes the conversation from interesting governance to buyer-grade control.
You can measure:
- Wrong-authority filing attempts refused before external exposure
- Supervised overrides with named accountability
- Refusal volume by workflow, role, and reason family
- Policy breakdowns revealed by refusal reason codes
- Downstream alignment between governed decision and execution outcome
You can show insurers, regulators, auditors, and internal oversight functions what was stopped, what was allowed, what was supervised, and why.
This is not just governance. This is a measurable ledger of bad actions that never happened.
Built For You If You Carry The Risk
If You Lead a
Law Firms
You can place one enforceable checkpoint in front of one high-risk filing or submission before it becomes an external event, without giving up legal judgment.
If You Lead a
Legal Department
You can show what was approved, refused, or routed for supervision under your organization’s authority, with a decision record your risk, audit, and leadership teams can review.
If You Lead Build
Legal Tech
You can add a mandatory pre-execution authority gate behind high-risk workflows without replacing your UI or exposing your internal logic.
The Architecture Behind the Control
The discipline of deciding whether a high-risk legal action may execute under authority, in context, before it becomes real.
The pre-execution control point where that decision happens
The fail-closed architecture that implements approve, refuse, supervised override and decision artifacts
The product that applies that architecture to your high-risk legal workflows
This is why SEAL does not behave like ordinary guardrails or after-the-fact monitoring. It governs the moment before the action becomes real.
Stop the wrong filing before
it leaves your firm — and prove it
SEAL gives you a narrow, reviewable, pre-execution control at the final submit boundary.
It does not replace your systems. It does not replace your legal judgment. It inserts one sealed checkpoint before one high-risk action leaves your firm, then records what happened in a sealed decision artifact.







