For Legal Tech Vendors
Add Pre-Execution Governance
Without Rebuilding Your Product
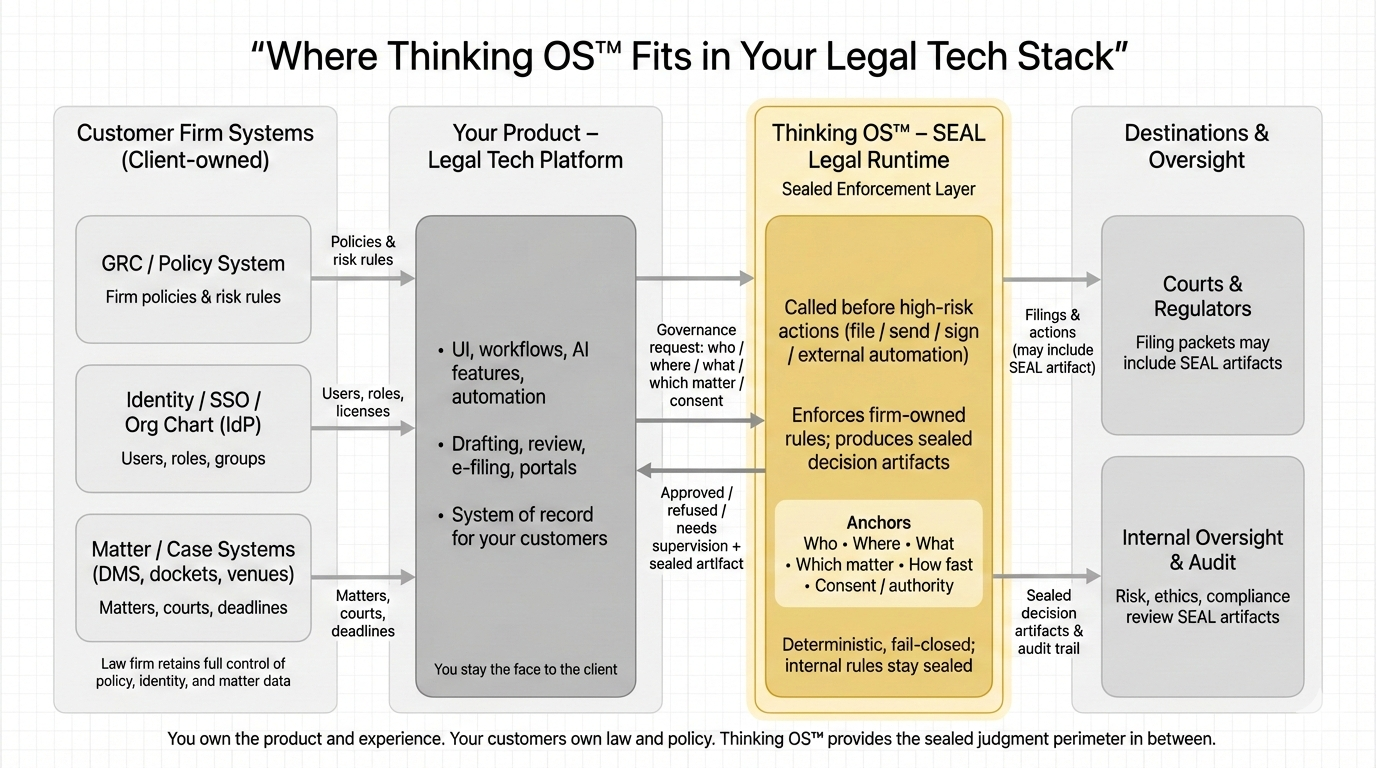
SEAL Legal Runtime gives your platform a sealed governance checkpoint before high-risk legal actions execute.
Your product keeps the UI, workflow, customer relationship, and system of record.
SEAL returns one governed outcome before the action proceeds:
Approve. Refuse. Supervise.
For every governed outcome, SEAL produces a reviewable decision artifact your customers can use
for legal, risk, audit, insurer, and oversight review.
The Question Your Customers Are Starting to Ask
Your customers are wiring AI and automation into legal workflows.
They still need to answer one question before a high-risk action leaves their environment:
Who was allowed to act, on what, under whose authority, and why did the system allow or stop it?
Logs are not enough.
Policies are not enough.
After-the-fact review is not enough.
Your customers need governance at the moment before execution.
SEAL gives your platform a way to support that without turning governance into a custom feature you rebuild for every enterprise deal.
What SEAL Adds to Your Product
SEAL inserts a pre-execution authority gate before designated high-risk actions.
Your product sends a structured intent to act. SEAL evaluates that request under the customer’s configured policy, role, authority, consent, and supervision posture. Then SEAL returns one governed outcome before the action proceeds.
Approve
The action may proceed. A reviewable approval artifact is produced.
Refuse
The action is blocked before it leaves the customer’s environment. A reviewable refusal artifact is produced with a clear reason category and rationale.
Supervise
The action cannot proceed on its own and must be reviewed or overridden by an authorized supervisor. That path is recorded too.
SEAL does not draft, file, send, advise, or replace legal judgment.
It governs whether a designated high-risk action may proceed under the customer’s rules.
Where SEAL Sits
SEAL is not another application your users need to learn.
It runs behind the scenes as a sealed governance runtime your product can call before designated high-risk actions execute.
Your product remains:
- the user experience
- the workflow surface
- the customer-facing system
- the system of record
- the place where users continue working
SEAL becomes the governance checkpoint between your product and the high-risk action boundary.
For workflows wired through SEAL, your product can require a governed outcome before the action moves forward.
The Architecture Behind the Control
Action Governance
= is the discipline
Commit Layer
= is the control point.
Refusal Infrastructure
= is the architecture.
SEAL Legal Runtime = applies it to high-risk legal actions.
What Changes — and What Does Not
Once SEAL is introduced, three things change.
Your product can send a governed request before selected high-risk actions.
Your product can receive an approve, refuse, or supervise outcome.
Your customer can receive a reviewable decision artifact showing what happened at the moment of action.
Everything else stays yours:
- your UX
- your workflows
- your models
- your prompts
- your customer relationship
- your commercial terms
- your roadmap
SEAL does not become part of your product identity unless you want that relationship to be disclosed.
It gives you a governance capability behind the workflow, not a new app your users have to adopt.
Why This Matters in Enterprise Deals
Your largest customers are going to ask harder governance questions.
They will want to know:
- which high-risk actions can your product initiate
- who is allowed to trigger them
- what authority or supervision is required
- what happens if the wrong user or system attempts the action
- what evidence exists after the action is approved, refused, or supervised
Without SEAL, your answer may depend on app logic, logs, admin settings, policy documents, or customer-specific workarounds.
With SEAL, your answer can be cleaner:
Your customer owns the rules.
Your product routes the governed action.
SEAL evaluates before execution.
The outcome is recorded in a reviewable artifact.
What Your Customers Can Verify
You do not need to ask your customers to believe a governance claim on faith.
For the workflow in scope, they can verify that:
- approval exists
- refusal exists
- supervision exists
- sealed decision artifacts exist
- fail-closed behavior exists
- the downstream gate exists
- scoped non-bypassability exists
This gives your platform a stronger answer than “we have logs.”
It gives your customers a reviewable control surface.
Proof Before Promises
Your customers do not want another governance slide.
They want evidence.
SEAL produces reviewable decision artifacts showing what the control did at the moment of action.
A serious evaluator can review:
- a governed approval
- governed refusals from different refusal families
- a supervised escalation path
- downstream alignment between the governed decision and action handling
- scoped non-bypassability for the workflow in scope
The public proof packet shows evaluator-visible behavior and evidence surfaces without exposing non-public runtime details.
Clear Responsibility Split
SEAL is designed to keep responsibility clear.
Your customer owns:
- legal policy
- authority rules
- identity and role sources
- matter and workflow context
- supervision posture
- legal judgment
- professional responsibility
Your product owns:
- the user experience
- workflow routing
- customer-facing operations
- how governed outcomes are surfaced
- how the product respects the returned outcome
Thinking OS owns:
- operation of the SEAL governance runtime within agreed scope
- faithful return of governed outcomes
- production of reviewable decision artifacts
- runtime security, availability, and isolation within agreed scope
SEAL does not decide what is legally advisable.
It enforces the customer’s configured governance posture at runtime for designated high-risk actions.
Data and IP Boundary
SEAL is designed for legal technology companies that cannot afford a messy data story.
SEAL works at the edge. It sees the minimum structured context required to govern the action.
SEAL
does not require DMS or database access.
SEAL
does not require prompt access.
SEAL
does not
tune on your models.
SEAL
does not use your customer’s matter data to train public models or improve other clients’ systems.
SEAL
does not expose non-public runtime internals as the assurance surface.
The assurance model is reviewable outputs, not exposed internals.
Your product stays yours.
Your customer’s legal work stays theirs.
SEAL provides the governed outcome and decision artifact.
Why Become a Confidential Evaluator
We are looking for a small number of legal technology platforms to evaluate SEAL in a narrow, controlled way.
This is probably relevant if your product touches workflows where customers care about:
- filing
- sending
- approving
- disclosing
- exporting
- submitting
- moving high-risk legal work outside the organization
As a confidential evaluator, you can assess whether SEAL helps your product answer enterprise governance questions with something stronger than policy language and logs.
You get a way to explore:
- governance as a product feature
- refusal as a trust signal
- sealed artifacts as buyer evidence
- pre-execution control as enterprise differentiation
This is not a big-bang partnership.
It starts narrow.
What a Confidential Evaluation Looks Like
A confidential evaluation is designed to be small, bounded, and practical.
The evaluation starts with one governed workflow.
Together, we identify:
- one high-risk action your product can initiate
- the customer governance question behind that action
- the minimum context required to evaluate the request
- the expected approve, refuse, and supervise outcomes
- the artifact story a serious buyer would need to review
The goal is not to rebuild your product.
The goal is to determine whether one governed action can be controlled before execution and supported with reviewable evidence.
If the fit is real, the next step is a narrow pilot.
How to Tell If This Is Worth Your Time
This is probably for you if:
- your customers are asking about AI risk, bar rules, governance, auditability, or authority
- your product can initiate or accelerate high-risk legal actions
- you are tired of solving “who may do what, under what authority” separately for every enterprise customer
- you want your answer to “what stopped this from going out?” to be stronger than “we have logs”
It is probably not for you yet if:
- your product only handles low-risk internal tasks
- your product does not touch filings, sends, approvals, disclosures, or high-stakes exports
- your customers are not asking for governance or evidence
- you are not ready to evaluate one narrow workflow
Without the Gate, Governance Stays Custom
Governance should not become a one-off feature request for every serious custom
r.
Without a pre-execution gate, vendors often end up adding more settings, more logs, more approval screens, more policy language, and more custom controls.
With SEAL, the pattern is cleaner:
Your product initiates the governed action.
SEAL evaluates before execution.
The customer keeps ownership of policy and legal judgment.
The outcome is recorded in a reviewable artifact.
That turns runtime governance from a cost center into a trust feature.
The Bottom Line for Legal Tech Vendors
You do not need to rebuild your product to answer enterprise governance questions.
You need a narrow, reviewable control point before your product allows high-risk legal actions to execute.
SEAL helps you move from:
“We have policies, permissions, and logs.”
to:
“We can show what was approved, what was refused, what was supervised, and what the control did before the action moved.”
That is the difference between governance as a sales slide and governance as a product advantage.

