In legal, the real risk isn’t just what a human or model says.
It’s what gets
filed, sent, approved, or executed under your name.
Most firms now govern:
- data (privacy, lineage, retention),
- models (testing, monitoring, guardrails), and
- security (identity, network, secrets).
All necessary. None of them answers the execution-time authority question.
What’s been missing is the layer that decides whether a high-risk action is allowed to run at all.
That missing discipline is
Action Governance.
That missing layer is the
Commit Layer.
The architecture category that implements it in legal is
Refusal Infrastructure for Legal.
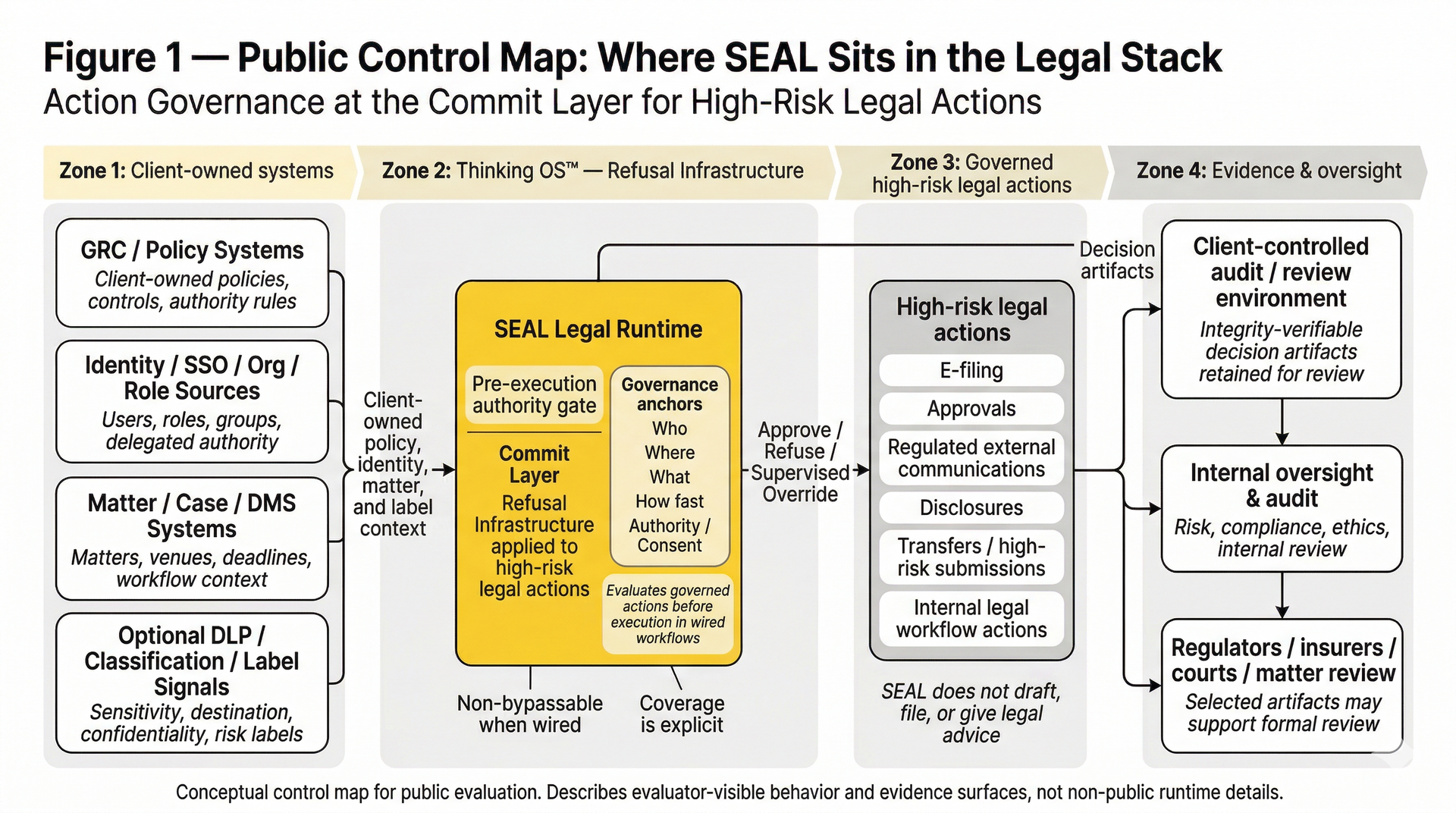
What Refusal Infrastructure for Legal Is
Refusal Infrastructure for Legal is a pre-execution authority gate in the Commit Layer for high-risk legal actions.
It sits between your internal tools and designated external actions or destinations and applies Action Governance before anything can be filed, sent, approved, or otherwise made real.
At runtime, it decides for each attempted action:
May this action proceed, must it be refused, or does it require supervision?
Instead of hoping training, policies, or dashboards will prevent bad outcomes later, Refusal Infrastructure enforces a pre-execution authority gate:
- Approve – the action may proceed under your rules.
- Refuse – the action is blocked and does not execute.
- Supervised override – the action is routed to a supervisor under your governance model.
This happens in wired workflows only—where the gate is structurally in the path of the action.
Action Governance: The First Principle
Every high-risk legal action ultimately turns on three core variables:
- Who may act
- On what
- Under whose authority
At runtime, SEAL evaluates those through five governance anchors:
who is acting, where they are acting, what they are trying to do, how fast it is meant to move, and under whose authority or consent.Action Governance is the discipline of enforcing these variables
at runtime, before a filing, communication, or other high-risk action leaves the firm.
Refusal Infrastructure for Legal turns that principle into a live checkpoint:
“Is this specific person or system allowed to take this specific action, in this context, under this authority, right now—approve, refuse, or route for supervised override?”
Where the Pre-Execution Authority Gate Sits
Refusal Infrastructure is not a plugin on your model. It is a governance layer at the execution boundary:
- Upstream of execution – before AI-assisted or human-initiated actions are filed, sent, approved, or otherwise executed.
- Downstream of identity and policy – after roles, verticals, and matter policies are defined in your own systems.
- Inside wired workflows – non-bypassable within the legal workflows that are routed through it.
If an action does not pass through the gate, it is outside the governed surface.
If it does pass through the gate, it is subject to
the same structural checks every time.
Wired Workflows and the Governance Boundary
Refusal Infrastructure is non-bypassable within wired workflows.
That means:
- For any workflow wired to the execution gate, there is no alternate “approve” path that skips Action Governance.
- Coverage is expanded by wiring more high-risk actions through the gate—not by claiming universal control over every system in the environment.
This boundary is what makes the promise credible:
- Clear in-scope actions (governed, non-bypassable once wired)
- Clear out-of-scope actions (not yet wired, visible through your broader governance program)
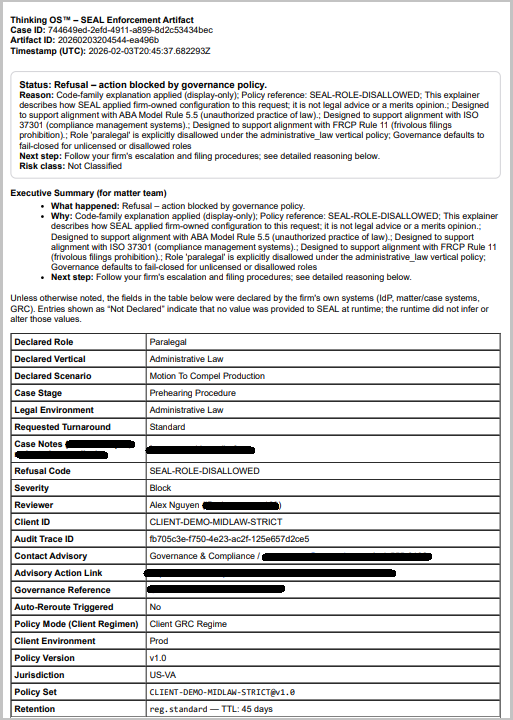
Sealed Artifacts: Evidence for Every Governed Decision
Unlike logging or monitoring, Refusal Infrastructure doesn’t just observe; it leaves behind evidence.
For every governed decision—approved, refused, or supervised override—it creates a sealed decision artifact:
- an integrity-verifiable record of who acted, what governed action was attempted, under which authority, and what verdict was returned
- designed for client-controlled audit retention and review
- structured for regulators, insurers, courts, and internal oversight
This is the difference between being able to describe your governance and being able to prove which actions were allowed to proceed under your seal.
Sealed Artifact, Not a Screenshot
Example refusal artifact (simulated realism testing).
A paralegal role attempted to file in a venue requiring licensed counsel. The pre-execution authority gate refused the action and produced a decision artifact showing:
- who attempted the action
- what governed action was attempted
- which policy context applied
- why the request was refused
This is the evidence surface legal teams can use for insurers, regulators, courts, and internal review — without exposing client matter content or model prompts.
How It Differs from Other Categories
Refusal Infrastructure for Legal is not:
- Identity and Access Management (IAM) – IAM governs access to systems (who can log in or see a resource). Refusal Infrastructure governs what actions may be executed, even by properly authenticated users or agents.
- Guardrails or model safety – Guardrails shape what a model can say. Refusal Infrastructure decides whether any resulting action is allowed to run at all.
- GRC platforms or policy portals – GRC tools manage documentation, attestations, and reporting. Refusal Infrastructure is the runtime enforcement point for those policies in live workflows.
- Monitoring or observability – Observability tells you what happened. Refusal Infrastructure determines what is allowed to happen.
It is a new layer in the control stack:
the Commit Layer — a pre-execution authority control for high-risk legal actions.
SEAL Legal Runtime: Refusal Infrastructure Applied to Law
SEAL Legal Runtime is Thinking OS™’s implementation of Refusal Infrastructure for Legal, purpose-built for law.
In legal workflows wired to SEAL Legal Runtime:
- Every high-risk action passes through a pre-execution authority gate
- Actions that are out of scope, missing required consent, or outside approved verticals are refused, not silently passed.
- Each governed decision leaves a sealed artifact designed to withstand regulatory, insurer, and court scrutiny—without exposing client matter content or model prompts.
SEAL Legal Runtime does not draft documents, provide legal advice, or replace attorney judgment.
It provides
refusal infrastructure and evidence so legal leaders can trust what their AI-driven stack is allowed to do.
Who Refusal Infrastructure Is For
For Law Firms and In-House Legal Teams
That want structural control over what can be filed, sent, or executed under the organization’s name.
For General Counsel and Risk Leaders
Who need more than policies and logs—they need a runtime gate and sealed artifacts.
For Legal Tech Vendors
That need a standard way to plug Action Governance into their products without rebuilding their models.
Thinking OS™ builds Refusal Infrastructure.
SEAL Legal Runtime applies it to high-risk legal actions.
It implements Action Governance by inserting the missing Commit Layer: a pre-execution authority gate in front of governed legal actions in wired workflows.
Before anything is filed, sent, moved, or executed, it returns Approve, Refuse (fail-closed), or Supervised Override (named accountability) and produces a sealed, integrity-verifiable decision artifact designed for client-controlled audit retention and review.
It is
not IAM, not model guardrails, and not a GRC platform.
It is a separate execution-time governance layer for moments where decisions must stand up to regulators, insurers, courts, and time.