One-line takeaway: The Commit Layer makes governance enforceable. It also exposes the adjacent layers you need so enforcement doesn’t collapse into bypass, drift, or post-hoc storytelling.
Why This Page Exists
Most “AI governance” conversations still collapse into one of two things:
- Formation: what systems are allowed to see and say
- Forensics: what happened after the fact
That’s necessary. It’s not sufficient.
As soon as AI can execute (file/send/submit/approve/move/change records), governance must include the missing control point at the moment before irreversibility:
The Commit Layer — a pre-execution authority control point that can Approve / Refuse (fail-closed) / Supervised Override (named accountability) and emit evidence.
Once you name and implement the Commit Layer, the rest of the stack becomes visible—and so do the gaps most organizations still treat as “someone else’s problem.”
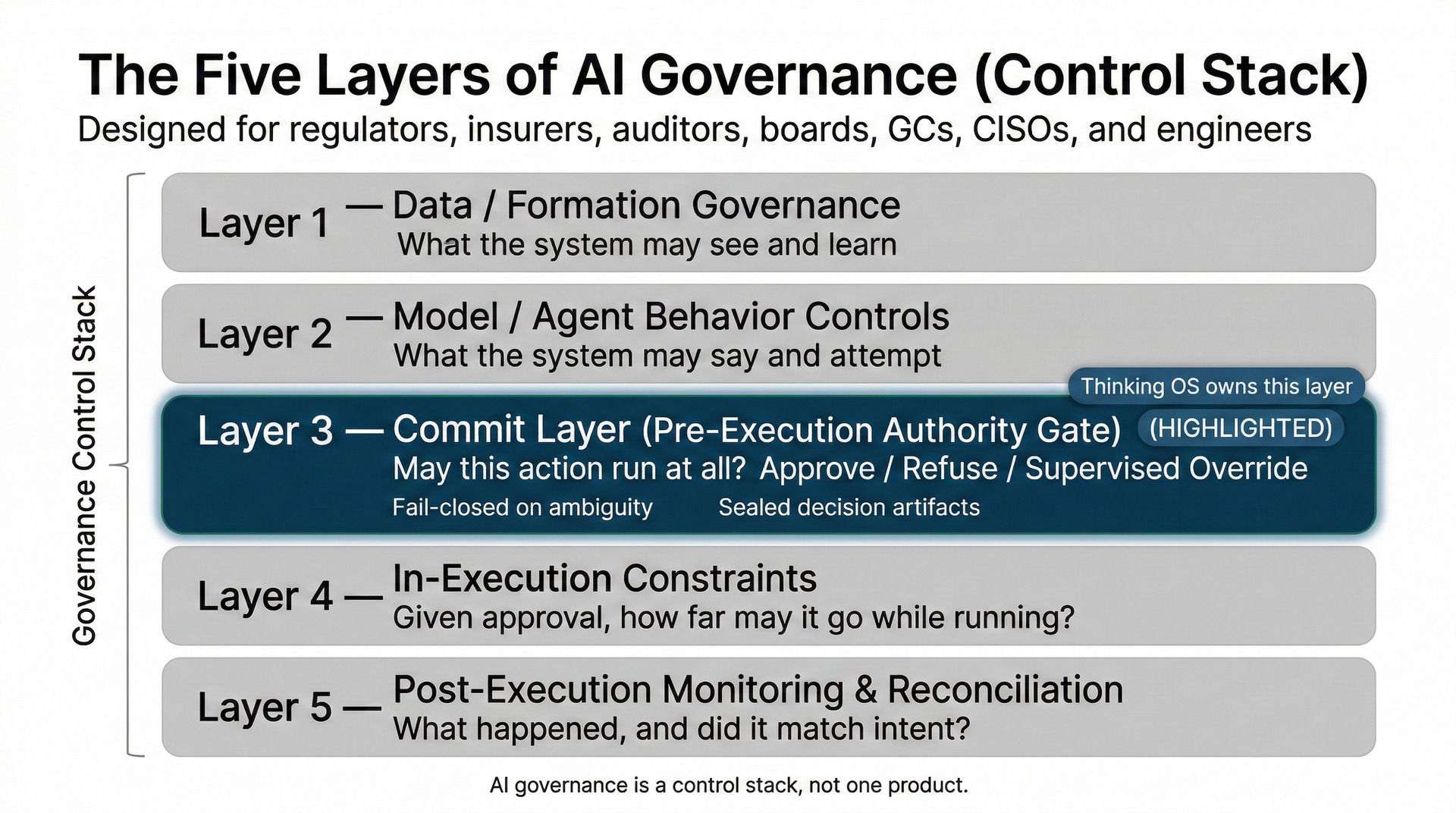
The Five-Layer AI Governance Control Stack
In serious environments (law, finance, healthcare, critical infrastructure), governance is a control stack:
- Data / Formation Governance
What the system is allowed to see and learn from. - Model / Agent Behavior Controls
What the system is allowed to say and attempt. - Commit Layer (Pre-Execution Authority Gate)
Whether a specific action may run at all—under authority, in context, right now. - In-Execution Constraints
How far an authorized action may go while it runs (limits, circuit breakers, step-up approvals). - Post-Execution Monitoring & Reconciliation
What happened and whether it matched intent; drift detection; audit/forensics.
If a vendor claims “we do AI governance” but can’t tell you which layer(s) they own, you don’t have governance. You have a feature.
Why Naming Layer 3 Exposes The “Missing Neighbors”
The Commit Layer forces a hard question at the execution boundary:
“For this actor, this action, in this context, under this authority—may it run at all?”
The moment you make that question real (and fail-closed), you also discover:
- who shows up without legible identity or delegated authority,
- which workflows never hit the gate (bypass),
- what happens after authorization (during), and
- how you prove outcomes match intent (after).
These aren’t theoretical. They’re the adjacent layers that determine whether an “enforced gate” stays enforced under pressure.
The Five Adjacent Gaps Most Stacks Still Don’t Treat as First-Class
1) Cross-org identity brokerage
Plain English: you can’t govern an actor you can’t identify.
- What it is: A way for external agents/tools to arrive represented inside the enterprise (firm-owned principal + delegation), not as anonymous callers with shared keys.
- Why it exists: Commit Layer decisions require a “Who” anchored to your IdP/authority model.
- Failure mode: External agents execute through side channels because no one established sponsorship or authority envelopes.
- Evidence signal: Sponsor chain + delegation context recorded (“who vouched, under what authority, for what scope?”).
What to ask: “How does an external agent become a governed actor—without turning API keys into ghost identities?”
2) In-execution constraints
Plain English: some actions are safe to start but become dangerous while running.
- What it is: limits, caps, circuit breakers, step-up approvals, escrow/staged commits.
- Why it exists: Approval is not a blank check; mid-flight drift is real.
- Failure mode: runaway tool loops, cascading edits, spend spikes, partial failures, uncontrolled retries.
- Evidence signal: constraint triggers + step-up events + override trails.
What to ask: “Once started, what stops it from doing too much, too fast, in the wrong direction?”
3) Post-execution reconciliation
Plain English: “intent approved” is not the same as “effect achieved.”
- What it is: reconciliation against systems of record to confirm outcomes match approved intent.
- Why it exists: external systems fail in partial and weird ways; toolchains introduce side effects.
- Failure mode: approved X, executed Y; wrong recipients; wrong records; wrong jurisdiction; partial state mutations.
- Evidence signal: mismatch reports + exception handling workflows.
What to ask: “How do we prove what executed matches what was authorized?”
4) Coverage mapping & bypass control
Plain English: if a workflow doesn’t hit the gate, it isn’t governed.
- What it is: a measurable map of governed vs ungoverned execution paths (and a plan to close bypasses).
- Why it exists: the biggest risks are undocumented integrations and shadow workflows.
- Failure mode: governance exists, but the action executes on an unwired path.
- Evidence signal: coverage map + bypass detection (“these actions never passed through a verdict”).
What to ask: “Show me all the ways a filing/transfer/approval could still happen without a verdict.”
5) Policy lifecycle governance
Plain English: if rules drift silently, enforcement becomes theater.
- What it is: versioning, change control, approvals, and auditability of authority rules and reason codes.
- Why it exists: policies are part of the control; mutable policies create mutable controls.
- Failure mode: exception creep, rubber-stamped overrides, “temporary” rules that become permanent.
- Evidence signal: policy versions tied to every decision artifact; controlled change history.
What to ask: “Who can change the rules—and how do we audit those changes?”
How The Commit Layer Strengthens “During” and “After”
Thinking OS does not replace Layers 4–5. It makes them credible by providing what those systems can’t invent later:
The moment of authority — who was allowed to do what, when, under which policy version, and why.
During (Layer 4)
In-execution constraints get cleaner triggers when authority is explicit.
If circuit breakers trip frequently for a class of actions, Commit Layer
artifacts show:
- which authority envelopes allowed them,
- which policies and versions were in force,
- what overrides were used (and by whom).
Result: you tighten the authority policy instead of arguing about “model behavior.”
After (Layer 5)
Monitoring can tell you what happened. The Commit Layer tells you whether it was authorized to happen.
That turns incident response from narrative reconstruction into decision-grade proof.
Where Thinking OS Stops
Thinking OS specializes in Layer 3: the Commit Layer (pre-execution authority + sealed decision artifacts). We intentionally do not claim to be “the AI governance platform.”
- identity providers (IdP/SSO),
- policy/GRC systems,
- matter/account/jurisdiction systems,
- optional data classification signals,
…and we answer one question ruthlessly:
“May this run at all—Approve / Refuse / Supervised Override—and where is the record?”
Partner Interfaces
If you want Layer 3 to work in a real environment, the interfaces matter.
Inputs the Commit Layer consumes
- Identity & roles (users, groups, service accounts; org chart)
- Policy & authority (rules, supervision requirements, consent envelopes)
- Context (matter/account, jurisdiction, environment, urgency)
- Optional labels (classification/DLP metadata)
Outputs the Commit Layer produces
- verdict: Approve / Refuse / Supervised Override
- sealed decision artifact: trace ID, anchors, verdict, policy version, reason codes
- routing signal for supervision and audit systems
- evidence surface for Risk Ledger / AI Risk P&L
Procurement Checklist: If You Have Layer 3, You Must Also Show A–E
If you’re adopting or building a Commit Layer, require these adjacent controls to be explicit:
A) Identity brokerage for cross-org actors
- How external agents become governed actors (sponsorship/delegation)
B) In-execution constraints
- Limits, circuit breakers, step-up approvals tied to governed action classes
C) Post-execution reconciliation
- Prove intent vs effect against systems of record; exception handling paths
D) Coverage map & bypass control
- Governed vs ungoverned execution paths; non-bypassable when wired
E) Policy lifecycle governance
- Versioning, change control, approvals; artifacts tied to policy versions
If any of A–E is “we’re hoping the vendor handles it,” your stack will bypass the gate or drown in forensics.
The Partner Stance
We specialize in Layer 3. We publish the full stack so the rest of your governance program can interface cleanly with the Commit Layer.
If you can’t name your other layers, you’ll either:
- bypass enforcement, or
- spend the next two years reconstructing incidents from logs.
- That’s the difference between governance-in-practice and governance-as-story.
Next Step
If you’re a GC or Managing Partner asking:
“How do we let AI assist with filings and approvals without losing control of who can let what run under our name?”
SEAL Legal Runtime is designed to be your answer.
